Enabling Single Sign-On
If your company supports single sign-on (SSO) using SAML 2.0, you can use your SAML 2.0 Identity Provider (IdP) to authentication your company’s users into the Vibes Mobile Engagement platform.
In this guide, we’ll provide you with the flow details and requirements to set up this integration. If you're interested in enabling single sign-on for your account, please contact your Vibes account manager.
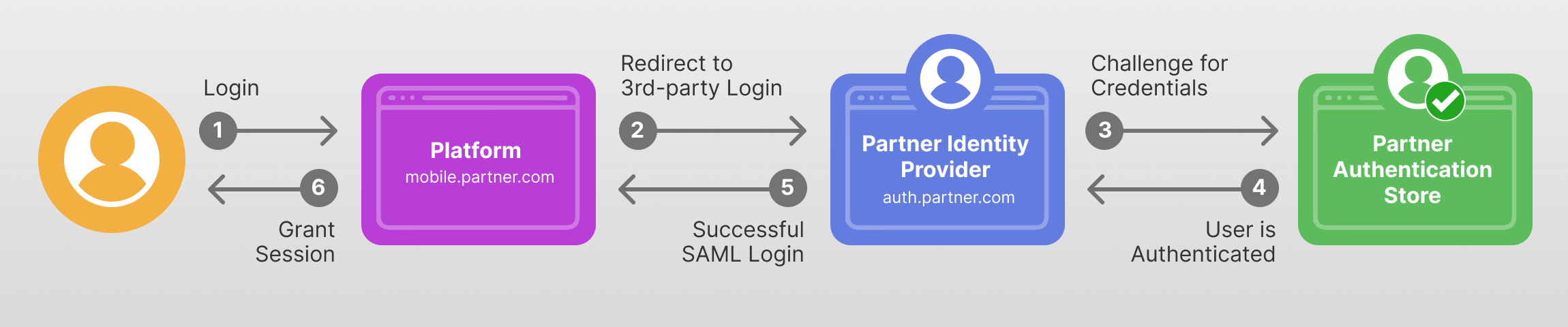
Flow Details
- User navigates to the Vibes Mobile Engagement Platform.
- User enters the email address associated with their platform account into the login page and selects Continue. The user is then redirected to your SAML 2.0 Identity Provider screen.
- User enters their username and password for your identity provider. Upon successful authentication by your IdP, the user is redirected back to the Vibes platform.
- The user is logged into the Vibes platform with access to platform modules based on their assigned permissions.
SAML Integration
To get set up your SAML integration, please provide Vibes with the following:
- The metadata endpoint for your SAML IdP. For example: https://sso.mydomain.com/saml/metadata.
- Optionally, the fingerprint of your signing certificate if you would like Vibes to verify it independent of the certificate or fingerprint provided in your IdP's metadata.
Once setup has been completed on Vibes' side, Vibes will direct users logging into the Vibes Mobile Engagement Platform to your IdP for authentication.
Vibes SAML service provider
- The metadata endpoint for Vibes SAML Service Provider is listed below. The metadata is signed.
https://auth.vibescm.com/saml/sp/<customer_federation_id>/metadata- The
entityidVibes uses is:
https://auth.vibescm.com/saml/sp/<customer_federation_id>The identifier Vibes expects back is the email address of the user. If your users don't have a unique email address, contact your Vibes account manager to discuss a custom solution.
Example
URN:OASIS:NAMES:TC:SAML:1.1:NAMEID-FORMAT:EMAILADDRESSSupported features
Web SSO:
- AuthnRequest - HTTP Redirect Binding.
- AuthnRequest - HTTP POST Binding.
- SAML Assertion - HTTP POST Binding.
XML Signatures:
- Metadata XML.
- AuthnRequests.
- SAML Assertions.
Encrypted Elements:
- Vibes supports encrypted elements in SAML Assertions.
User timeouts
Vibes' user timeout period is 24 hours of inactivity. After 24 hours of inactivity, Vibes will re-authenticate using your identity provider.
Additional validation
Only users that are configured for third-party authentication will be accepted from the customer identity provider. Other users will receive an invalid authorization error.
Updated over 1 year ago